Post PetyaWrap - How To Prevent Ransomware Attacks
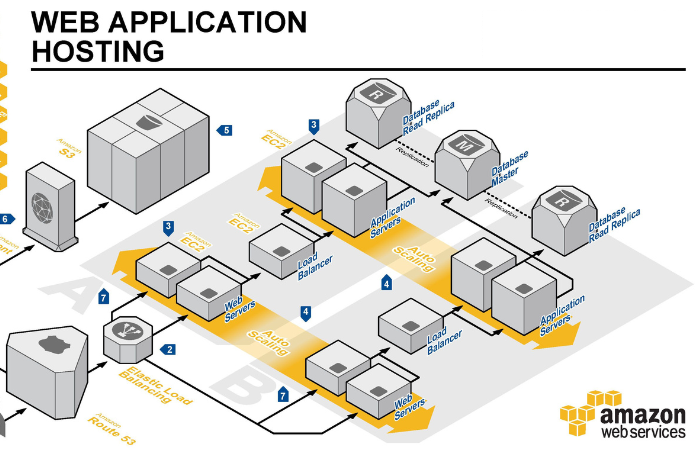
Now that most have recovered from the hangover of the PetyaWrap ransomware attacks, it is Monday morning quarterback time. PetyaWrap was not a new ransomware with a zero day vulnerability, but rather a combination of three common vectors of attack that companies do not always take seriously. But securing your assets go beyond just your servers (aka EC2 instances); you also need to ensure your AWS Account is equally as secure.