Continuous Security Monitoring
Automate & Streamline Compliance
Multi-Framework Support
Smart Remediation
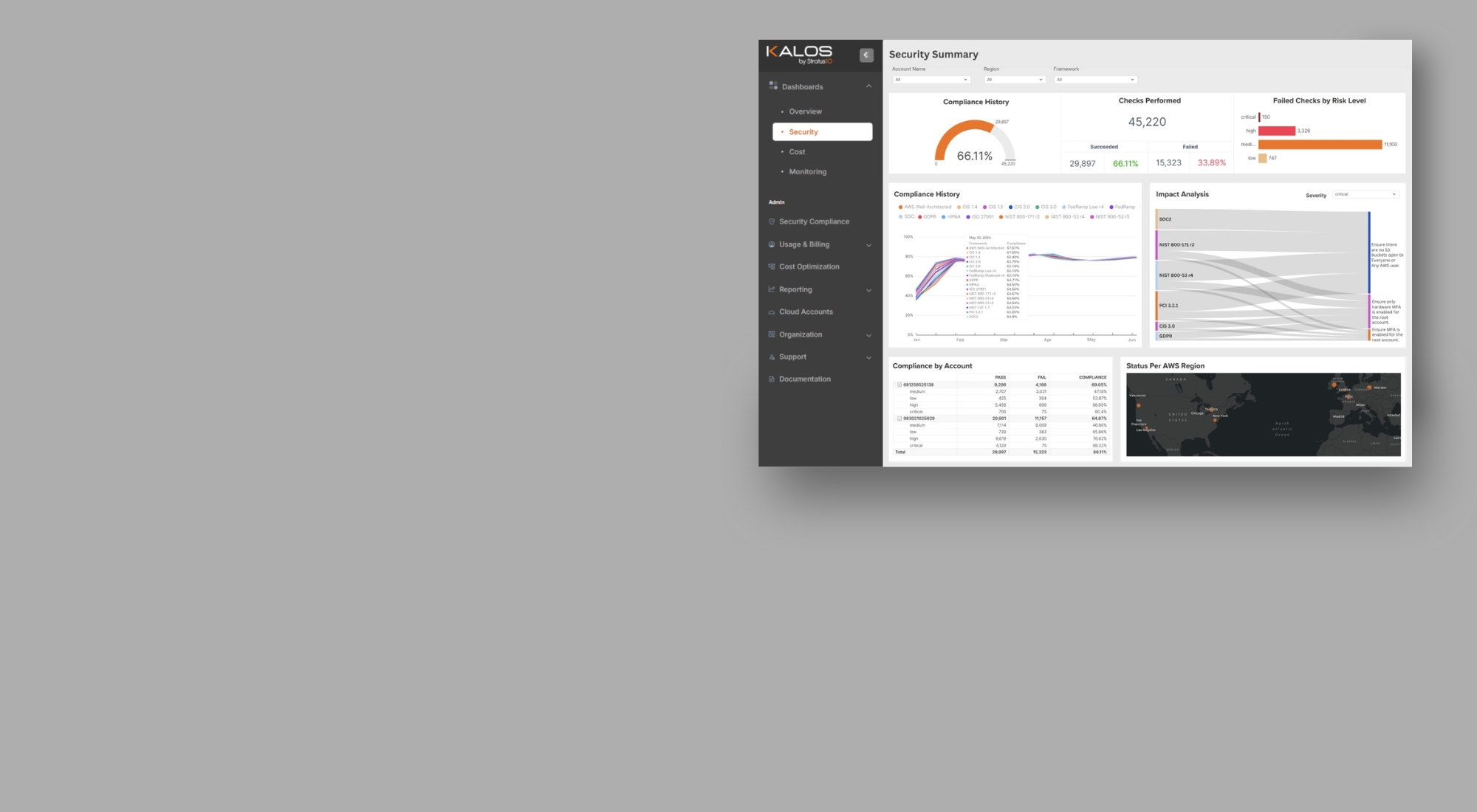
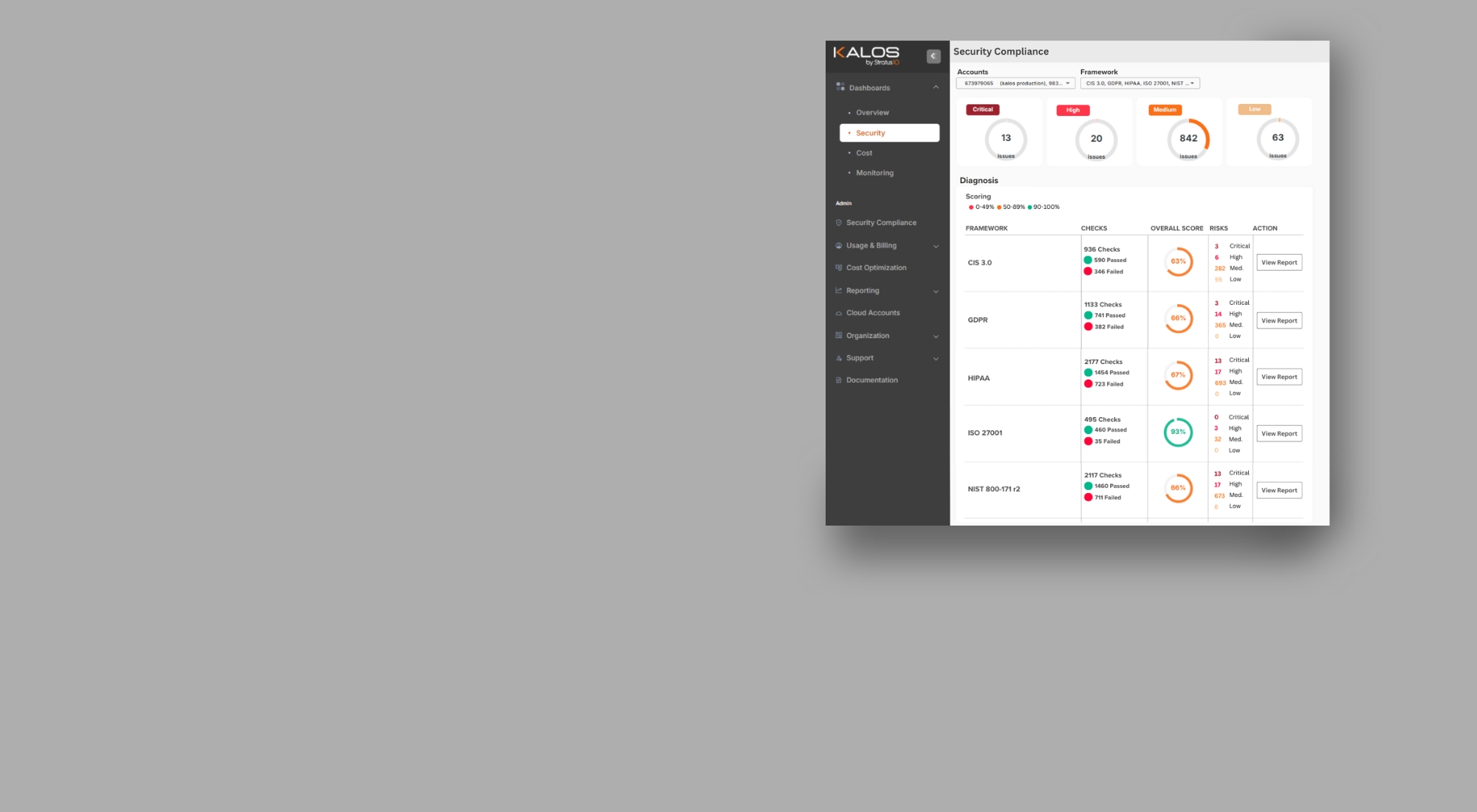
Real-Time Compliance Insights
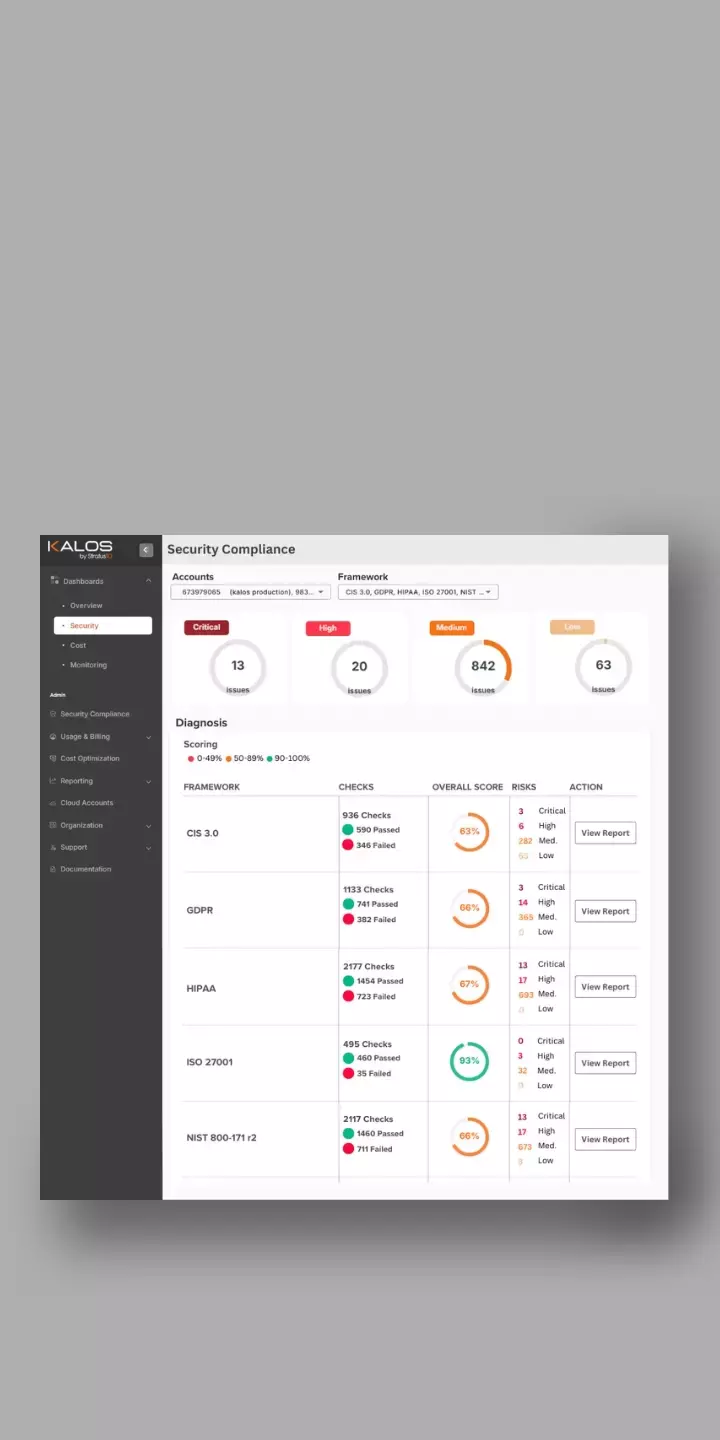
Cloud Compliance Control Center
Automated Compliance Monitoring
Unified Compliance Dashboard
AI-Powered Recommendations
Seamless AWS Integration
Prioritized Impact Report
Cost Optimization & Monitoring Dashboards
Supported Frameworks - All Included

SOC2
Establishes criteria for managing customer data based on five "trust service principles"—security, availability, processing integrity, confidentiality, and privacy.

ISO 27001
The internationally recognized standard for information security management systems (ISMS), ISO protects sensitive data through risk management and robust security controls.

HIPAA
Ensures the confidentiality, integrity, and security of healthcare-related data, protecting patient information and setting rules for its handling and sharing.

FedRAMP
Low r4 and Moderate r4 provide security controls for cloud systems that handle low-impact data and sensitive federal data, respectively.

PCI DSS 3.2.1
Ensures the secure handling of credit card information through strict technical and operational standards, protecting cardholder data from breaches and fraud.

GDPR
Sets comprehensive data privacy regulations for organizations handling personal data of EU citizens with strict requirements for consent, processing, and protection.

NIST
800-171 r2, 800-53 r5, and CSF 1.1 specify security requirements for protecting Controlled Unclassified Information (CUI) in non-federal systems and outline controls for federal systems to protect sensitive data.

CIS
Provides security guidelines specifically for AWS cloud environments, offering best practices to ensure the secure configuration and management of AWS infrastructure.

Dedicated Cloud Expertise, On Demand
Dedicated Cloud Expertise, On Demand
Cloud optimization isn't a one-time task; it’s a continuous process. That's why you also receive expert consultation, implementation, and real-time troubleshooting for your AWS environment. With a dedicated Customer Success Manager and expert engineers by your side, we ensure you have the ongoing guidance needed to optimize your cloud infrastructure.
For more in-depth optimization, we offer project-based work to align with your evolving needs. And with our Premium tier, you get full-service, hands-on-keyboard infrastructure management, ensuring that your team always has the resources to meet critical business objectives.
From day-to-day guidance to long-term cloud strategy, we’re here to support you every step of the way.

Available on the AWS Marketplace
Simplify your trial sign-up by procuring directly through the AWS Marketplace.
Resources
Whether you're ready to explore a demo, curious about how we can help, or eager to start a free trial, we're here for you.
Fill out the form, and our team will get back to you with the information you need.